Full disclosure: Whilst I obtained a copy of RoyalTS/Server via the MVP program, I was in no way obligated to write this article. Nor did I receive any reward for it. This is my experience after a real incident that I should have done something about sooner.
Okay, so as some of you might know, my home lab recently got hacked. The long story short is I had RDP open to the Internet and despite having a domain controller and updating most of my passwords when they appeared on https://haveibeenpwned.com/ whoever found an account and dropped malware encrypting my lab and demanding a $6000 ransom. (Ha no. Never pay these people!)
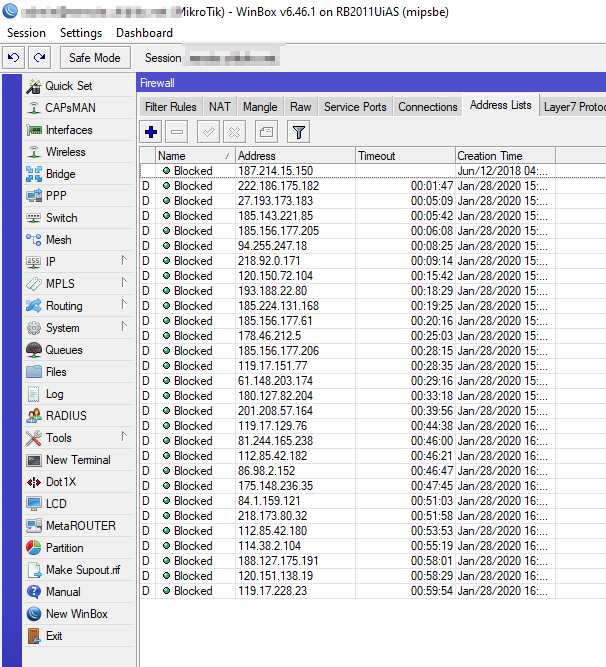
It turns out I had used an old password when building the server years ago and had forgotten about the local admin password when updating account passwords (GirlGems would kill me) and my automatic blocking script on my Mikrotik did nothing about it as it only detects port scans, not bad logins
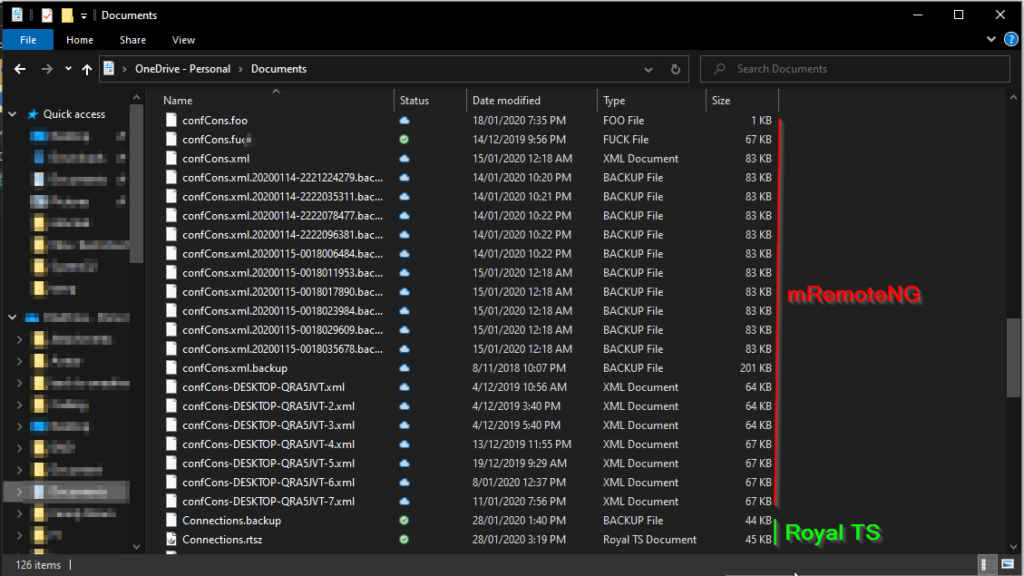
The stupid thing was, I was actually in the process of moving from RDP and mRemoteNG over to Royal TS and along with it Royal Server thanks to a free license as part of the MVP program. I just figured I’d leave RDP open for a little while longer.
What happened?
See the issue with RDP based access, especially if you leave the default port of 3389 open is that every mother and his dog will just start password spamming your Windows box, and by default, it will do nothing about these attempts. So unscrupulous attackers will simply blast known username/password combos at RDP until something sticks and once they are in, it’s game over.
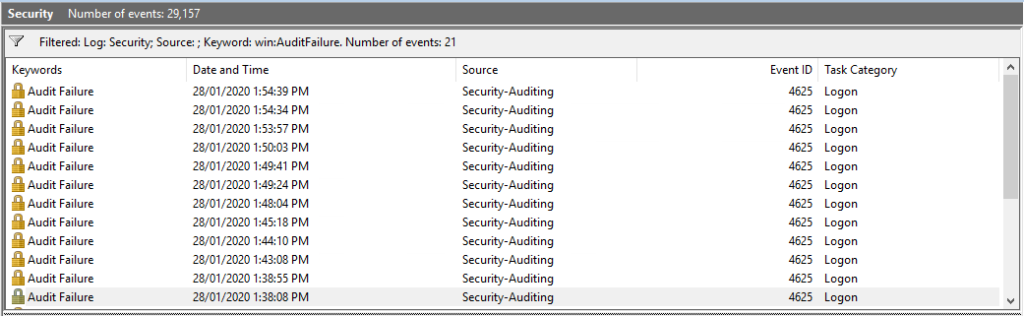
So, just for giggles, I re-opened RDP to the Internet for 15 minutes. And I was getting connection attempts almost instantly, 21 failed connections and I haven’t even been online for long so haven’t been found by many attackers (I had a screenshot of my box getting hammered at the time, but I’ve lost it)
So how does Royal TS / Server solve this?
First off, Royal TS by itself doesn’t solve this by itself, it similar to mRemoteNG in that it supports a multitude of protocols like RDP, VNC, SSH, and Webpages. But along with Royal Server, it can manage services directly discouraging the use of RDP in the first place.

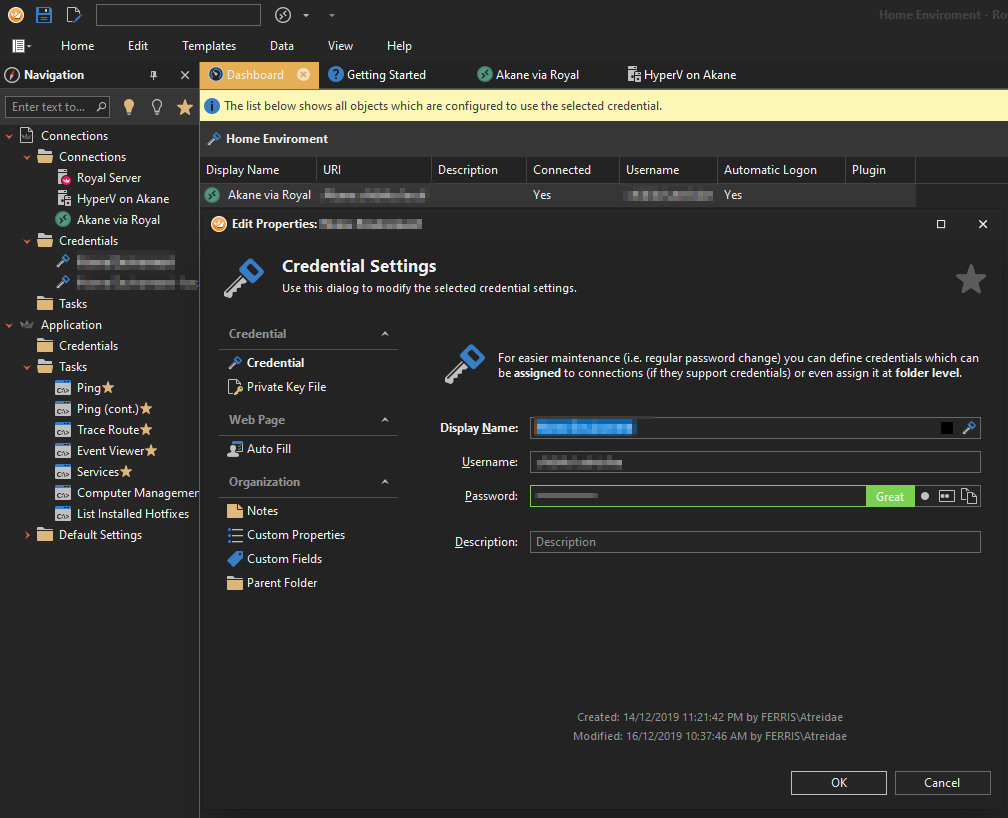
And we can even store our creds in a secure manner and reuse them for servers in the same environment (Great for when you change the password)
It also won’t corrupt your connections file if you store it on OneDrive like mRemoteNG as it is OneDrive aware and will force sync every time it changes
It even supports multi-user mode so multiple people can have the connection file open at the same time, with auditing on who created and changed what.
If you’re after that Quick Connect bar like in mRemote. Simply click Home and Right-click > Add to Quick Access for both the Ad-hoc text box and the dropdown menu.

Voila, quickly connect to anything RoyalTS supports just the same as mRemoteNG
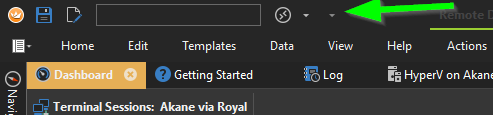
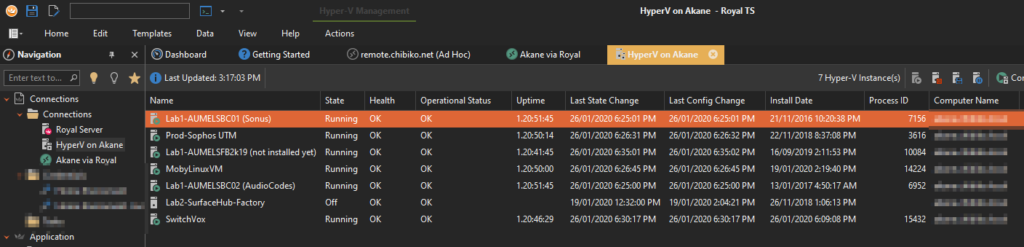
Did I mention it can let you manage Hyper-V and connect to machines directly without having to be domain joined / RDP into the Hyper-V Hypervisor?
Yeah but RDP is still open James?
Yes, we know, and that’s where Royal Server Secure Gateway joins the fight. This is basically a simple to manage SSH port tunneling setup built into Royal TS/Server for you. No need to remember complex setups and run Putty to invoke ports.
You simply set up all your connections as you normally would whilst you are on the LAN, and as long as your Royal Server has the same hostname internally and externally you can connect via a secure SSH tunnel.
Setup is easy and lets me connect to services using Royal TS in a few clicks.
I just need to enable the server, Add users and tell Royal TS the gateway exists.
In Royal Server we simply need to click On Secure Gateway > Enable Royal Server Secure Gateway and set any ip addressing (internal) we like
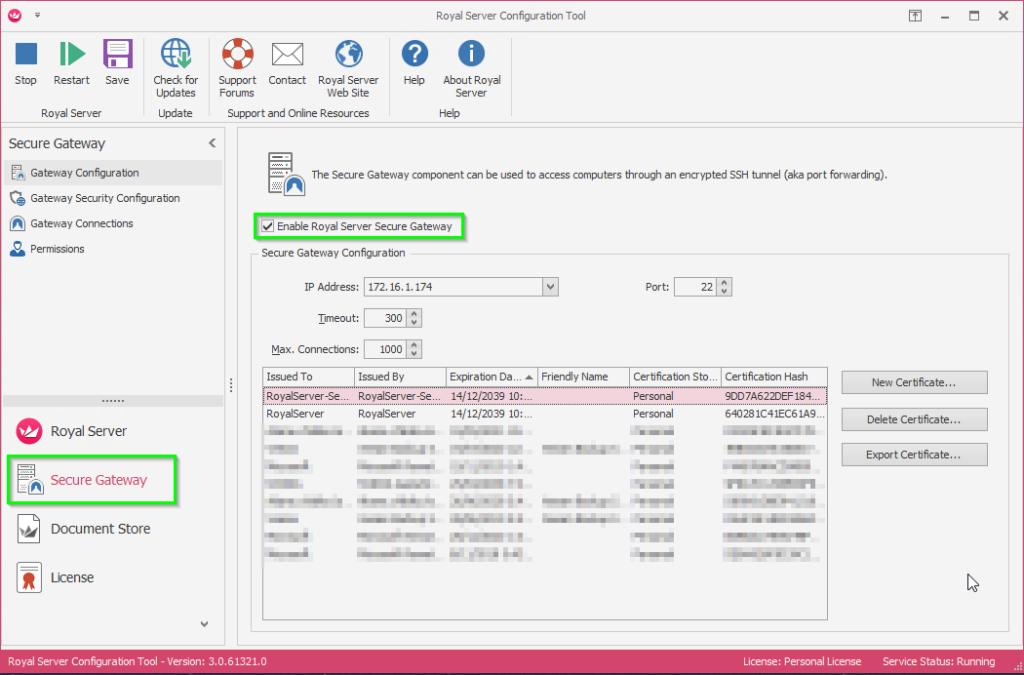
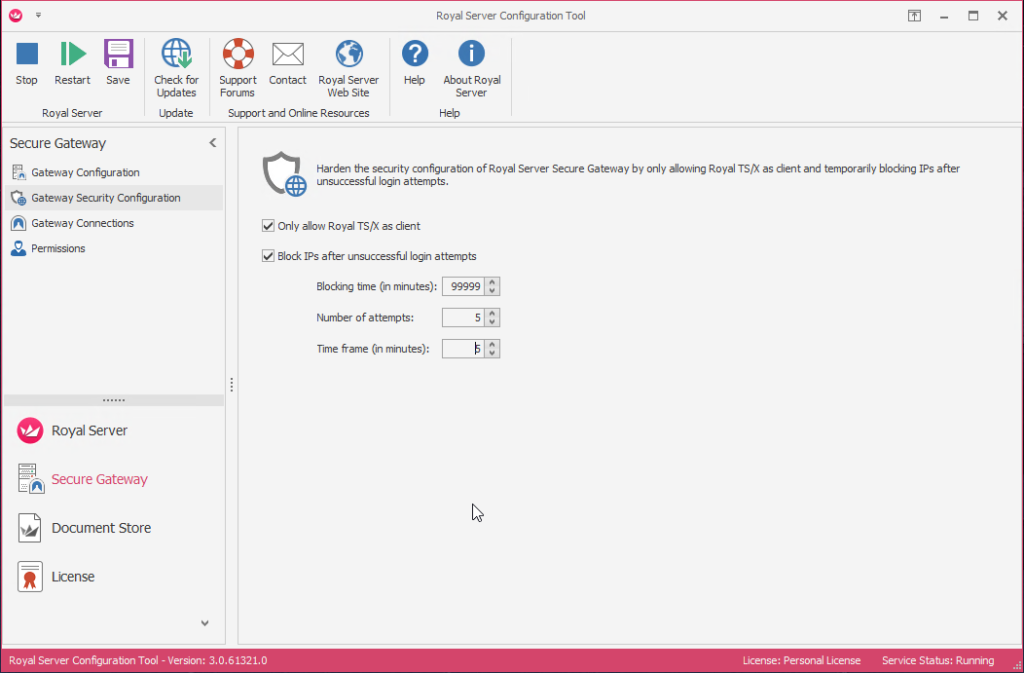
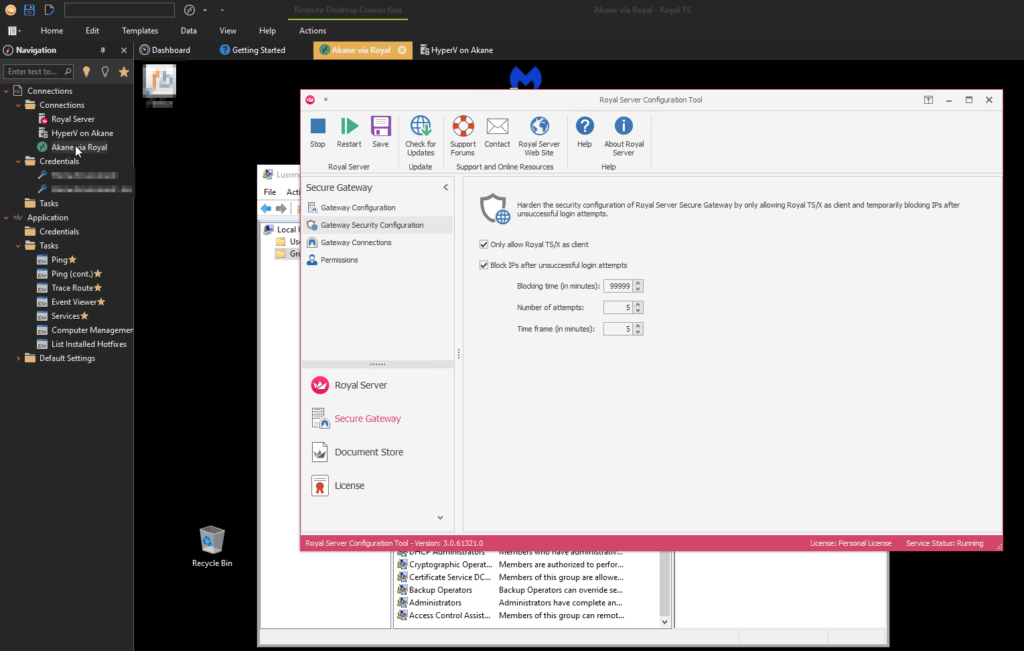
Then on the Gateway Security Configuration page, I enabled Only allow Royal TS/X as a client and setup an autoblock
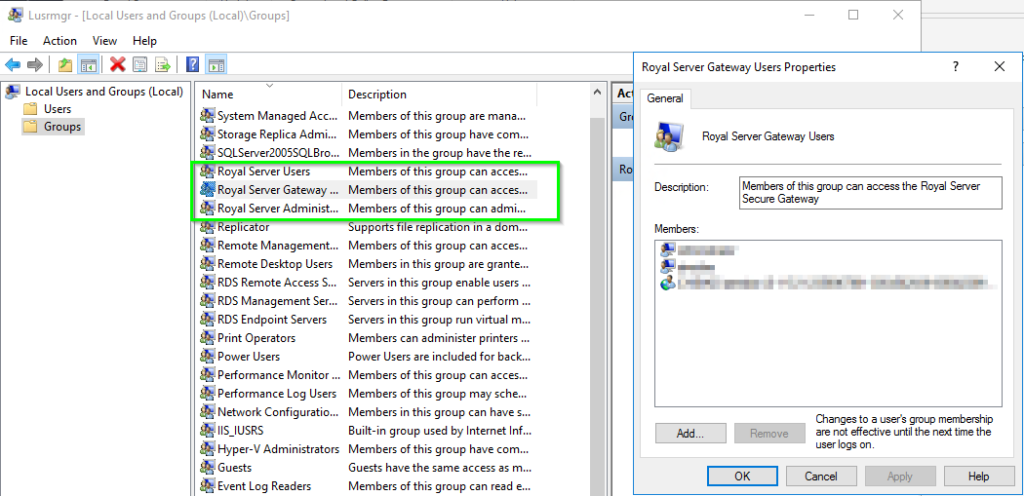
We then need to enable users to use the gateway, Open lusermgr.msc and add the desired users to the Royal Server Gateway Users, Royal Server Administrators, and the Royal Server Users groups.
Port forward both ports 22 and 54899 to your Royal Server host using your router and your Royal Server is online. (Don’t forget Windows Firewall)
Setting up the client
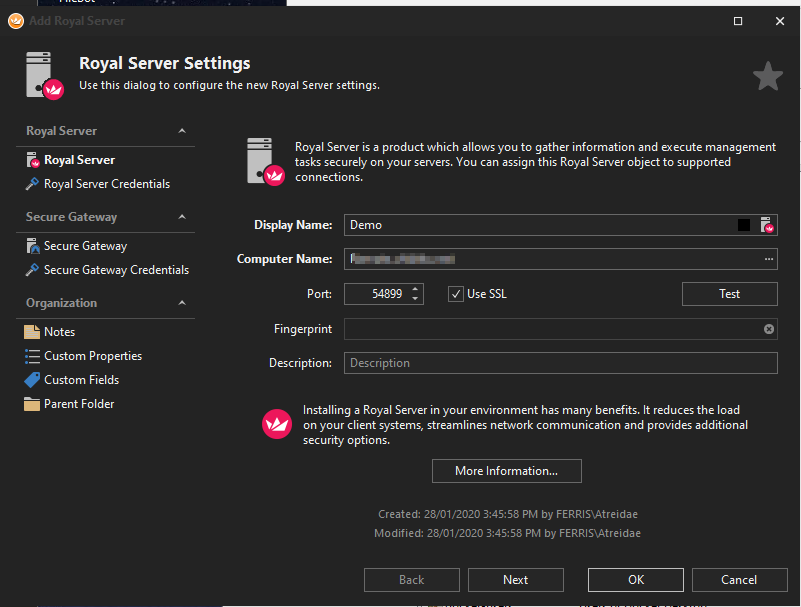
In Royal TS add a new connection of the Royal Server type, filling in the WAN address of your network, adding a credential and testing
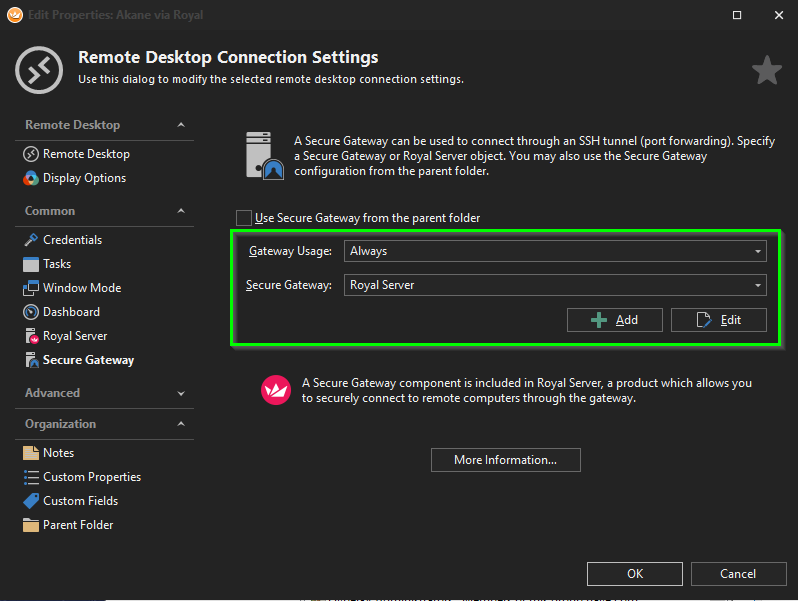
Now in your Royal TS connection to that box, simply select Always under gateway usage and select the Royal Server
You can now double click on your connection to be connected through the SSH tunnel automatically.
Once that’s working, you can close 3389 on your external firewall and not worry about being compromised ever again. If anyone does hit the SSH port (and they do, a lot) Royal Server will block them after a few attempts anyway.
If you’re after more information you can check the Doco here and feel free to try it out for yourself. I’m not getting any affiliates/referrals etc from it and the free version isn’t bad on its own either. Check it out over here