I came across an interesting one recently whilst setting up Kerberos for a Skype for Business 2019 build.
As part of the standard build, I created a Kerberos account in the customer’s OU and assigned it to a site without error. But I did notice a tiny little warning that “Site 2” wasn’t in the topology.

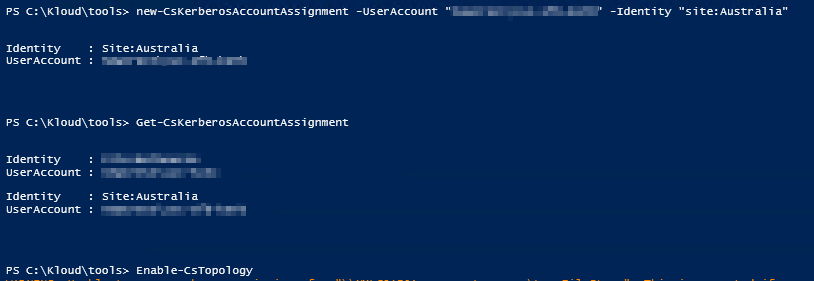
So we quickly checked for the account, yep its there and assigned
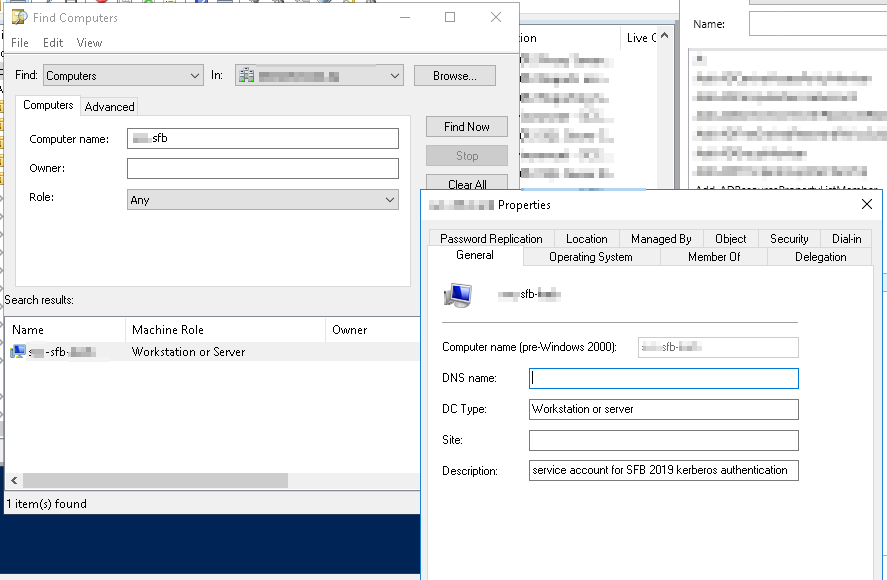

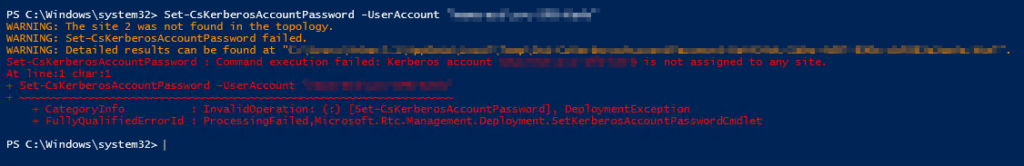
But attempting to set the account password fails with the error message
1 | Kerberos account ucmadscientist\derpy is not assigned to any site. |
Another check of topologies verifies we have no Site 2.
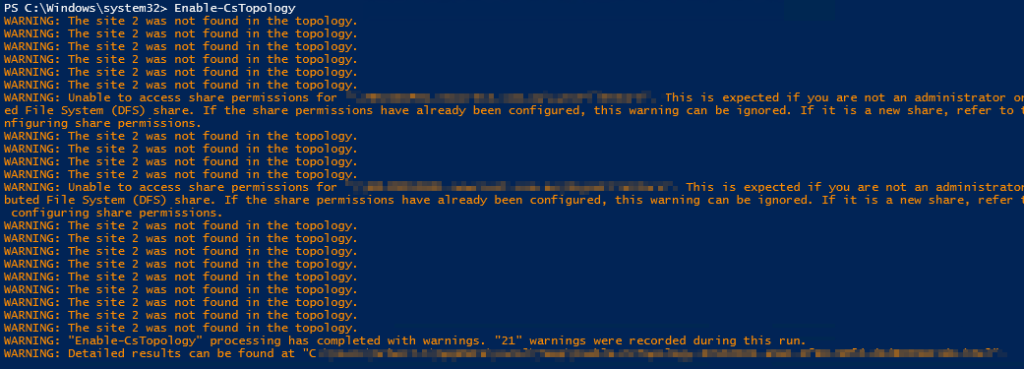
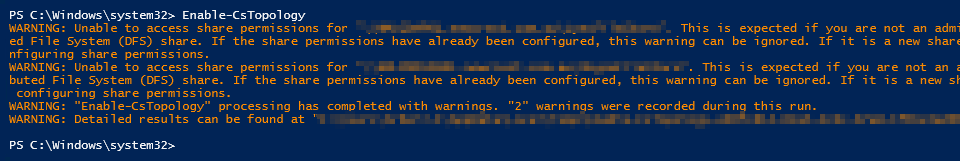
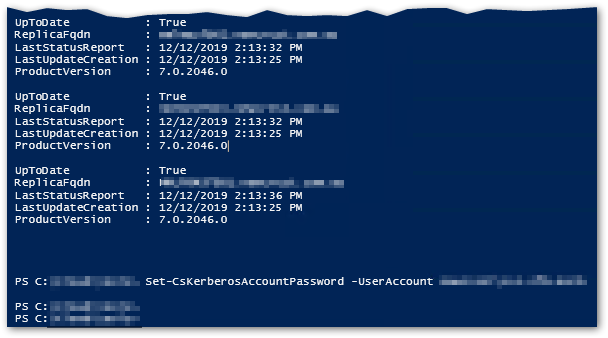
But running Enable-CsTopology at the shell throws warnings re Site 2 (these didn’t show up in Topology Builder)
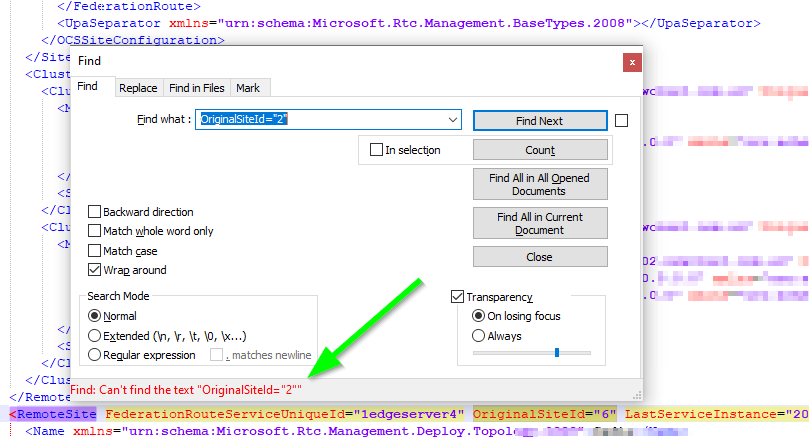
I even downloaded and searched the TBXML for OriginalSiteId=”2″ and OriginalCluster=”2 (note the lack of a trailing quote mark is intentional as any cluster ID’s would be after this) just to be sure.
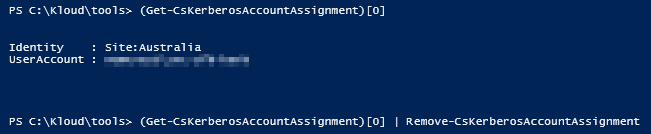
But the eagle-eyed among you might have spotted there is still a Kerberos account assigned to Site2 (hence the warning). So let’s remove that with a bit of code to select the relevant object and remove it
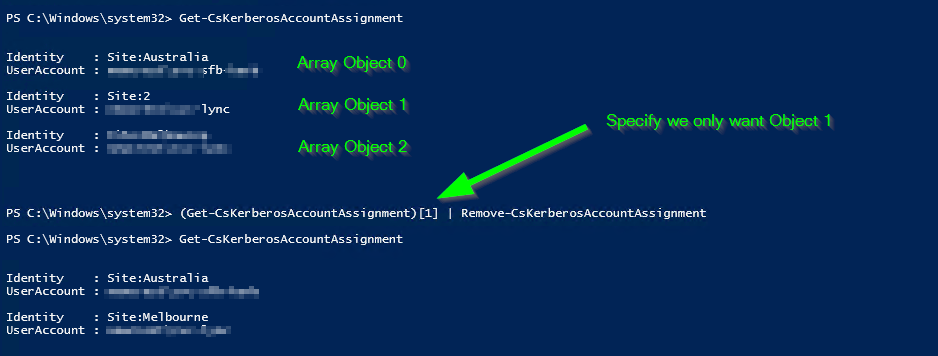
1 | (Get-CsKerberosAccountAssignment)[1] | Remove-CsKerberosAccountAssignment |
You can now see we no longer have a Site:2 defined in our Kerberos assignments and we can now assign the account without warning.
Enabling the Topology no longer throws warnings about site 2 either
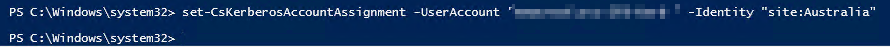
Now we need to remove the Kerberos association entirely and create it again using Remove-CsKerberosAccountAssignment and New-CsKerberosAccountAssignment
Note: Using Set-CsKerberosAccountAssignment doesn’t appear to fix it.
Then publish the topology with Enable-CsTopology
Wait for successful replication and then you can set your Kerberos password as normal.
Hope this helps someone!