Hey, Remember that AudioCodes review I did waaaaay back in August then got distracted with PowerShell stuff?
Well I’ve had some time to spend working with the unit as well as talking to AudioCodes about the solution in general. Quick Shout out to David at AudioCodes and the guys at Auroz for letting me hold onto this demo unit so long. Thanks guys.
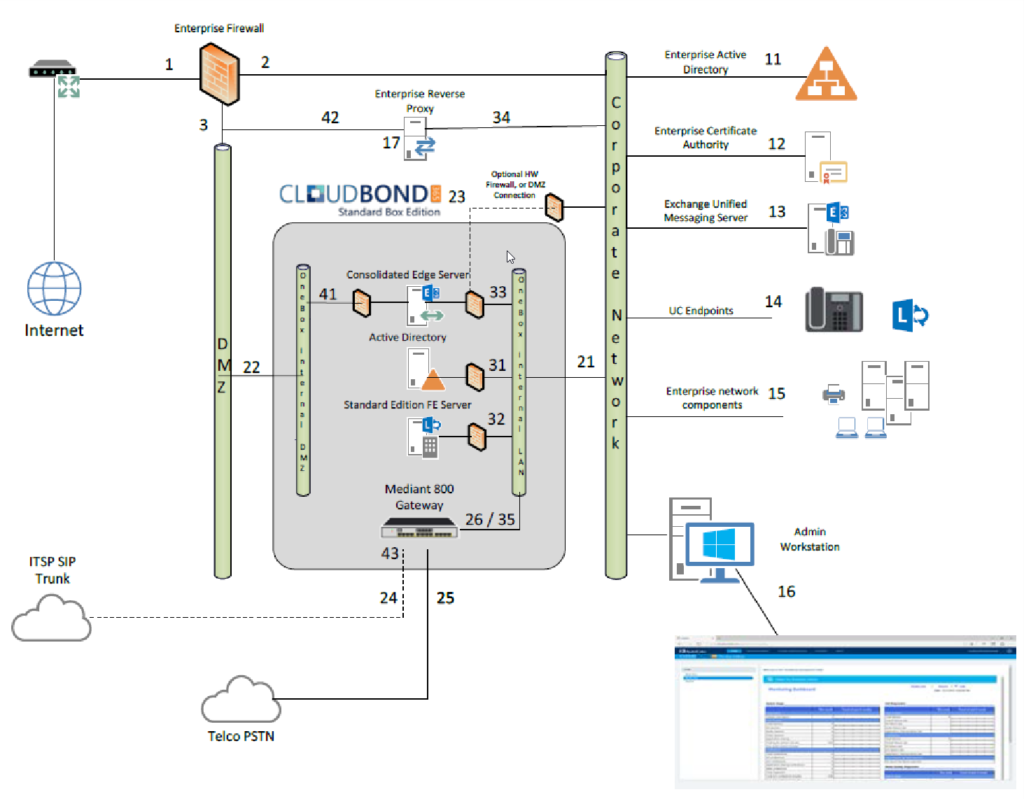
In case you didn’t see it in my last article, the AudioCodes CloudBond is a “Pre-built” Skype for Business On-Prem or Hybrid instance in a box that comes with its own Domain Controller, Front End and Edge server. Higher end units also include things like a reverse pirate proxy (IIS ARR) and SBC. Standard units do however come with a Mediant 800 gateway built in instead of the SBC.
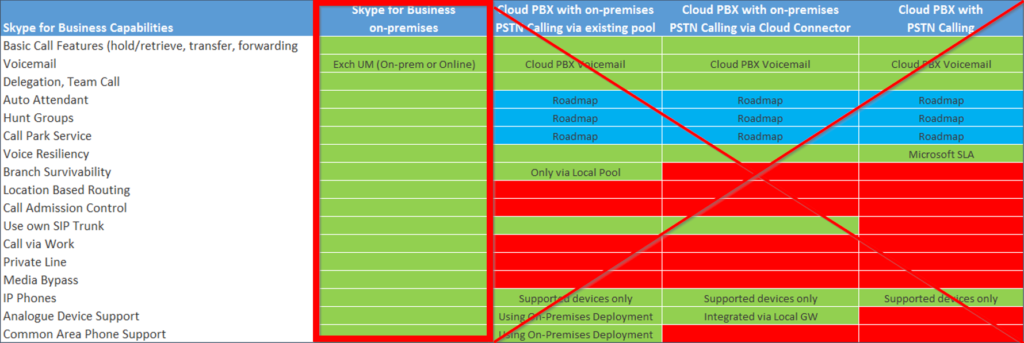
I need to point out it is NOT Cloud Connector Edition. AudioCodes have a different product for that and I’m not going to cover that here right now. But, because this is a full on-prem Standard Edition deployment with a Real SQL instance it means you get the full Skype for Business suite, including CDR and QoE (I haven’t tested CQD on it yet)
- Response Groups? Check!
- Auto Attendant, Call Groups? Check!
- Trusted Applications? Check!
- CAC, Call Via Work, Media Bypass? Check!
To give you an idea, here’s an image from the manual showing how the CloudBond fits into your existing deployment assuming you have an existing AD infrastructure. Everything inside the grey box is handled by the CloudBond itself. Making life easier for both the customer and the UC architect.
As the unit comes in a few variants I’ll point out I’m playing with one based off the Mediant 800 SBA.
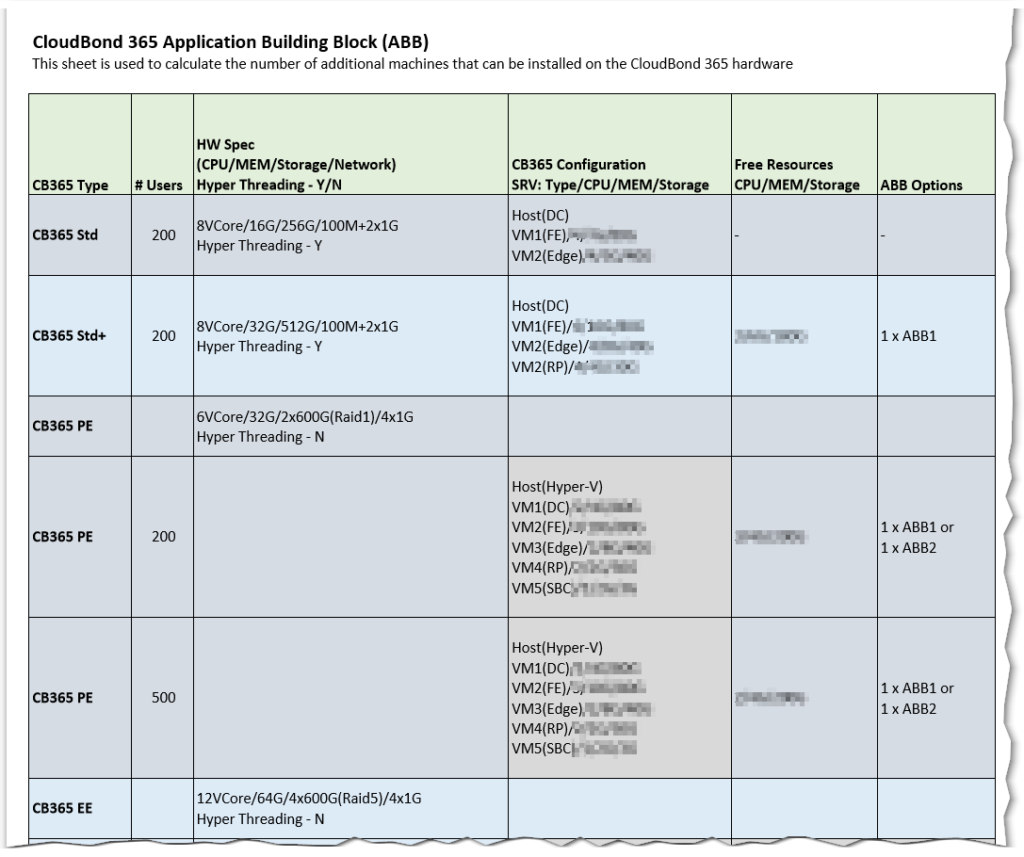
One of the great things they really don’t point out is there is spare room on the appliance that you can stick your own applications on.
Need another VM to run a trusted app server or maybe a Polycom FTP? Yep. Got you covered there.
In fact I recently worked on a proposal where we were looking to co-locate Enghouse on one of the larger units.
AudioCodes has thought of everything here and if you’re a partner they even provide specs on what resources are available to your additional VM’s. AudioCodes call these Application Building Blocks
The magic of the prebuilt environment is though AudioCodes excellent setup software, the fact it runs its own domain controller and the web interface that removes end users from any of the AD/SQL/IIS/and Skype backend. The environment isn’t locked down either. Need to jump into the traditional Skype4B control panel? There’s a link right there. Want to RDP into any of the boxes? Yep you can do that too.
Think of it as an AudioCodes SBA for a full Skype4B build. They built an excellent web interface, but still let you get into the backend if needed.
- You can set it up on its own and have a Skype4B deployment in a single RU appliance (or 2RU if you run paired pools)) with nothing external. Even if the customer runs a full Mac environment
- The cloudbond runs its own AD controller and has a brilliant interface for adding and removing users. No knowledge of AD is required.
- You can bolt it into a customer that’s pushed everything into 365 and no longer has any form of domain onsite Using AADSync or manually import users here
- You can plug it into an existing AD environment via a forest trust, replicate users into the “local” Audiocodes domain with it writing all the RTC attributes back into the customers’ existing AD
It’s been created by someone who understands both how Microsoft sees UC working and how traditional PBX guys see a system like it.
ie: “Plug a box in, configure extensions. That’s the phone system” (Sorry Greig, I like old PBXes too)
What’s even cooler is that AudioCodes looks to be releasing a Virtual version for deployment on your own VM infrastructure instead of using their dedicated hardware making the need for UC guys for smaller deployments along with 365 Cloud PBX more and more redundant.
Other cool things include a copy of Veeam to back everything up, you can also order the unit with additional Veeam licences to backup your extra machines (ie, your trusted app server)
Okay, maybe I should actually show you some stuff rather than it just reading like an advert?
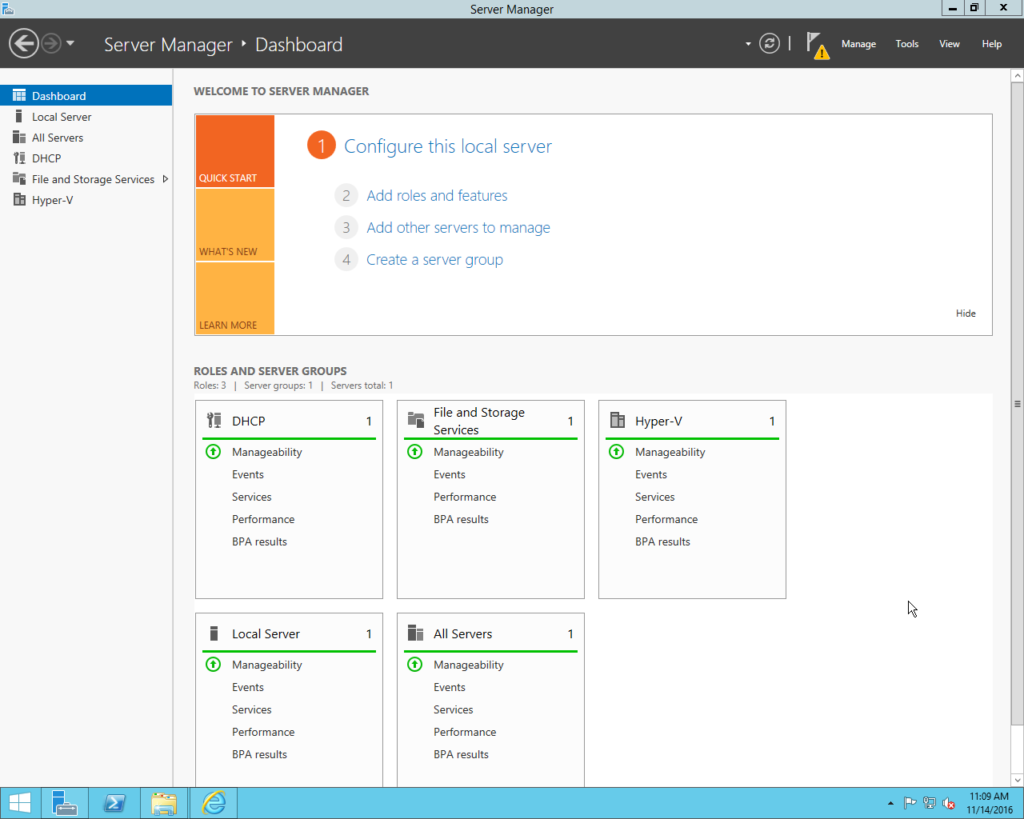
As I pointed out in my last article, My unit was a trial unit that had already been to another customer and it came to me in a pretty sorry state. After re-installing the OS from the included recovery media I was dropped back to a Windows Desktop complete with Server Manager
We’re going to quickly run through the Skype Environment setup process assuming you know where most things in windows server are.
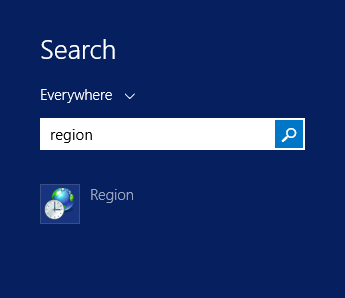
The first thing you want to do is set all the region options and the date and time options as the automated installer skips these options
First, Search for Region in the start menu and open the Region control panel item
Change both the Formats and the Location to your local region and click OK
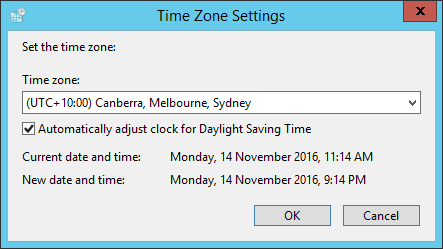
Update the Timezone and Time appropriately using the normal windows methods
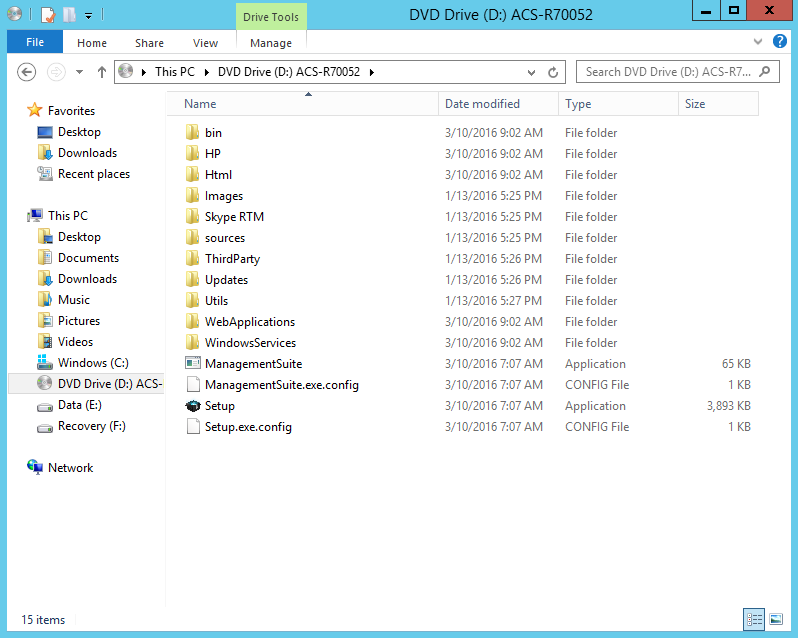
Once the boring stuff is done you can head on over to the CloudBond installer located on the Recovery partition F: and double click on the “ACS-(Version Number)-Skype-RTM-SQL-Std.iso”
I assume this iso may change based on the options ordered so your mileage may vary.
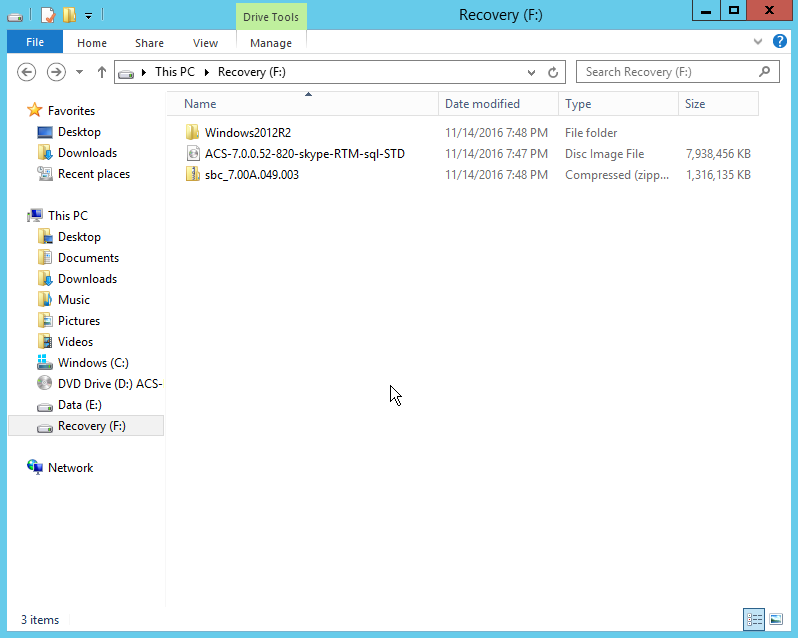
This should Automount the ISO as D: and you can run the installer Setup.exe
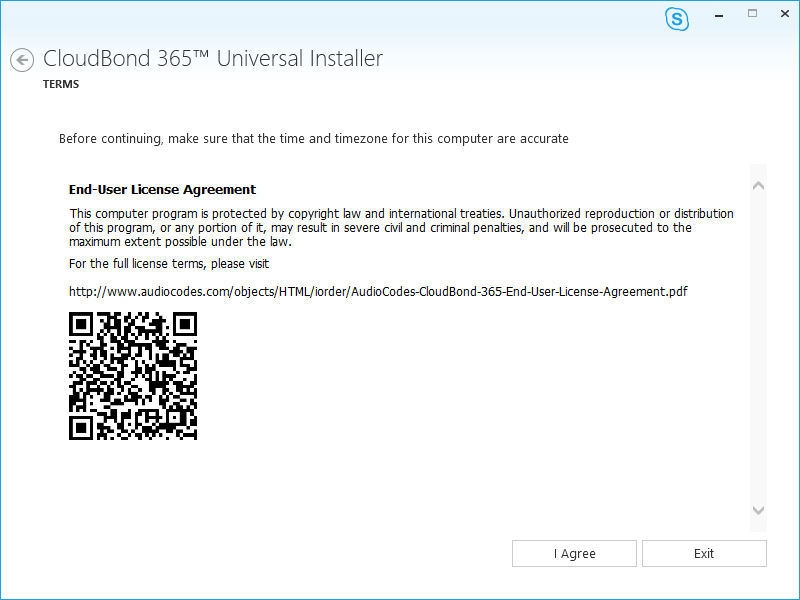
We get dropped into a EULA confirmation screen as well as a reminder for us to set the date and time.
A nice touch here is the EULA has a QR code that you can scan and email the PDF to a customer instead of forcing them to read the URL off a screen in the server room.
Grab the URL if you need it and hit I Agree
As I mentioned before the unit supports being in a paired pool scenario, I’m not sure if you can pair this with an existing Skype4B deployment or if it’s just with other CloudBond units
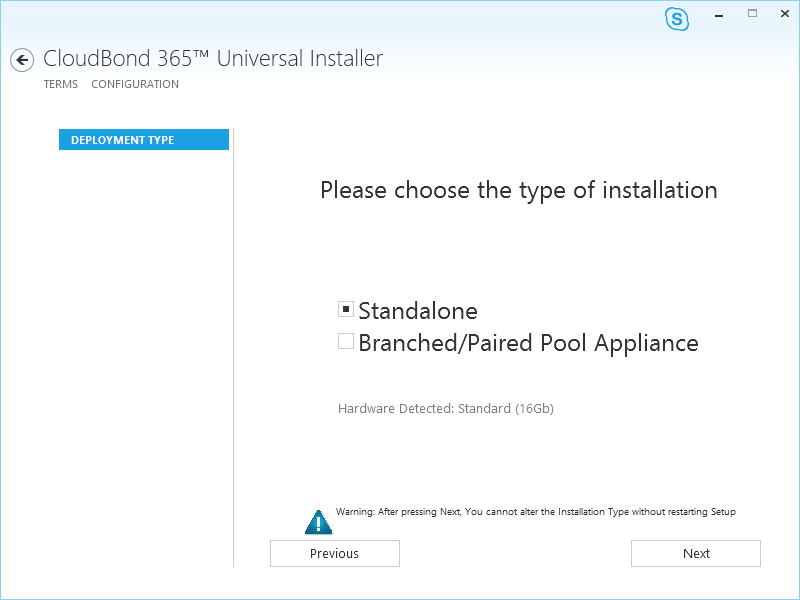
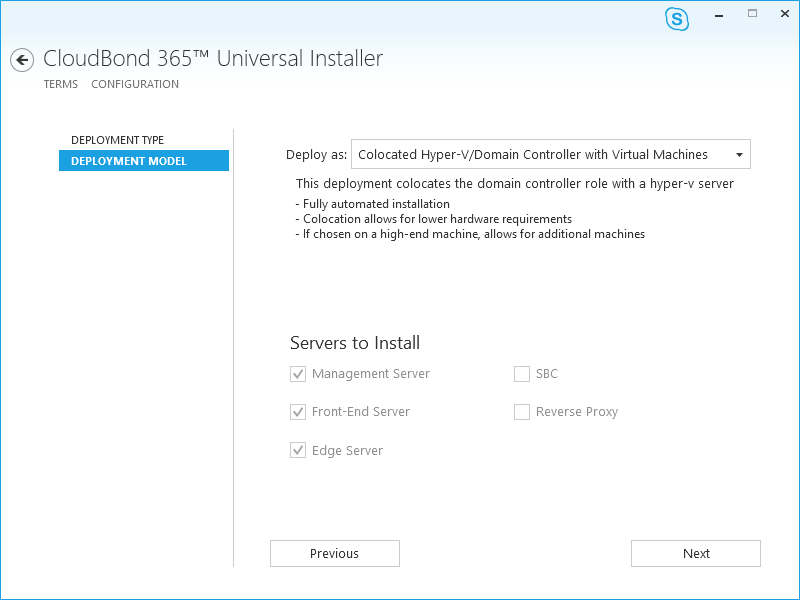
Depending on your hardware level you get a fair few deployment options, as I’m on the base unit I’m restricted to the defaults, We don’t need an SBC as the M800 has a dedicated gateway module anyway, but I will need to setup my Watchguard as the reverse proxy.
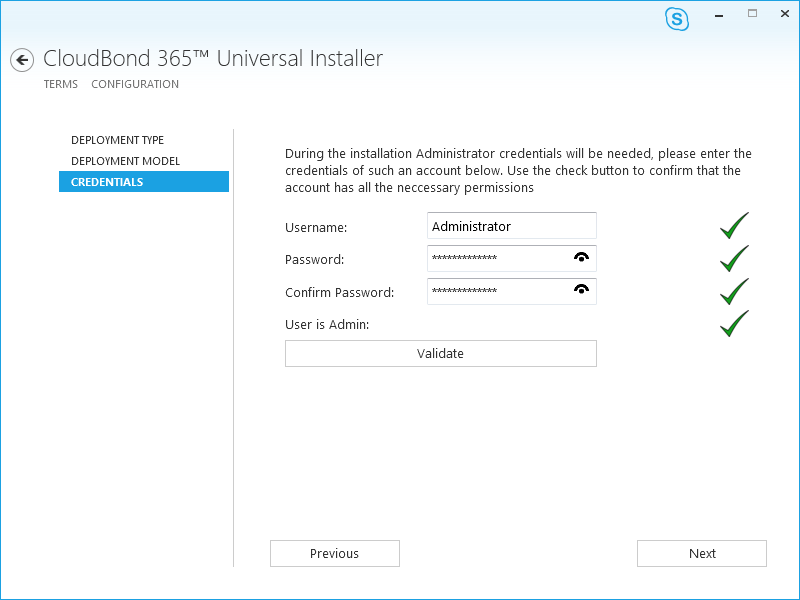
The usual credentials screen, as this was a standalone unit everything was filled in here.
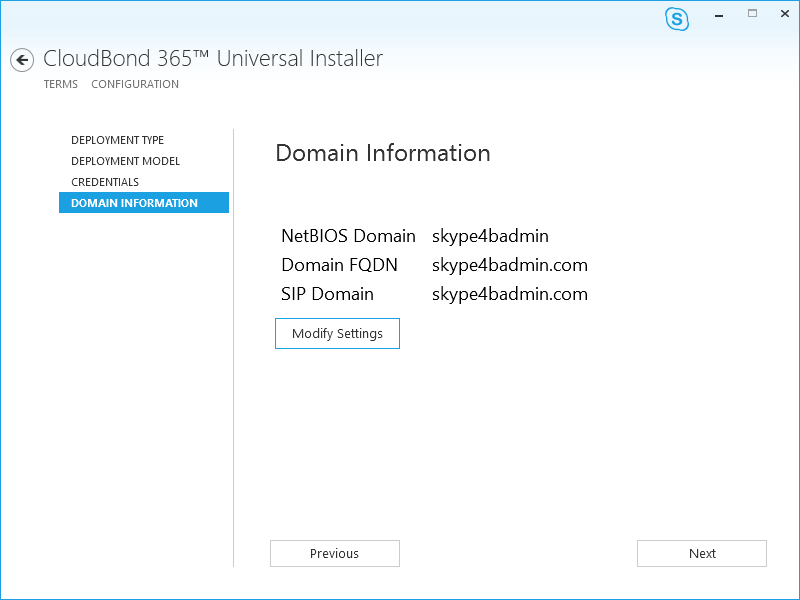
Now we setup the information of the internal domain on the CloudBond. You would need to refer to the documentation in a Forest Trust setup, but for standalone I just configured it as Skype4badmin.com
Now we setuo the details of the “Management Server” on the M800 that’s the base machine acting as the Hyper-V host for the extra machines. It installs the required roles locally and then builds the Skype VM’s as guests on itself. I image the “Virtual” edition when it launches would build a separate DC VM
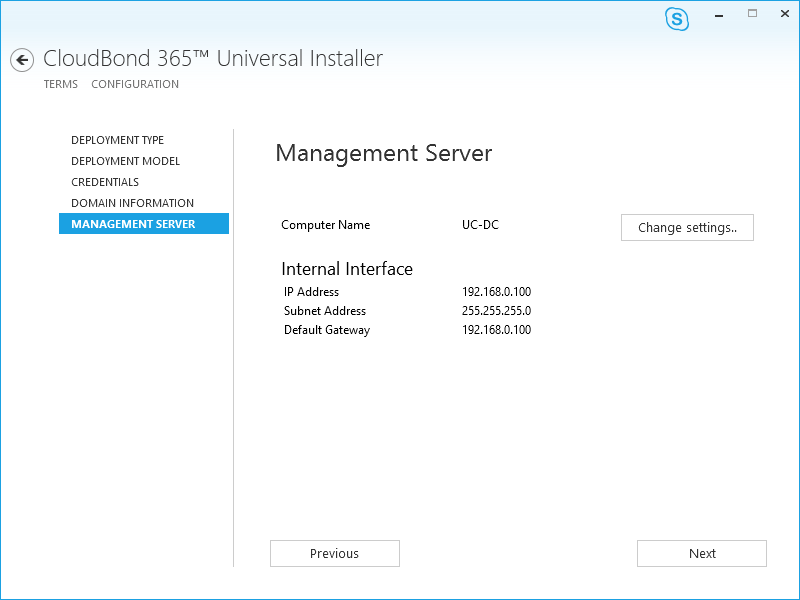
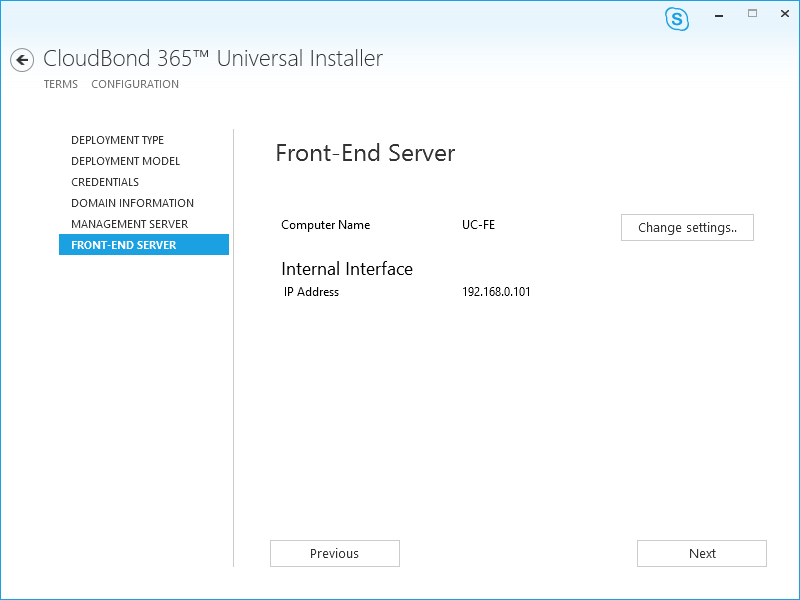
Now we define the FE’s internal IP/hostname, I left all these at defaults for the review.
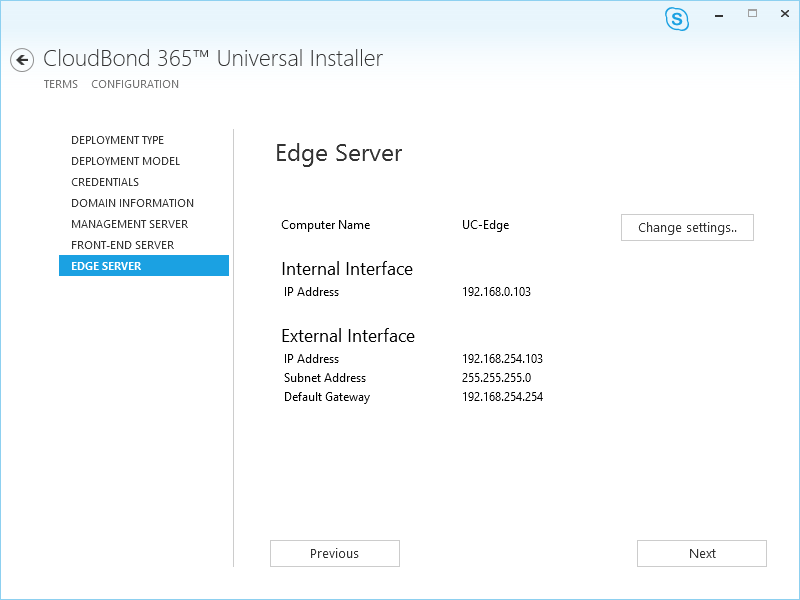
Now, the Edge server. You can see here it’s using a consolidated edge with a single external edge IP address. So some external users behind weird firewalls may have issues connecting to the edge. I’ve seen banks and stuff that won’t allow HTTPS traffic on port 445 for example.
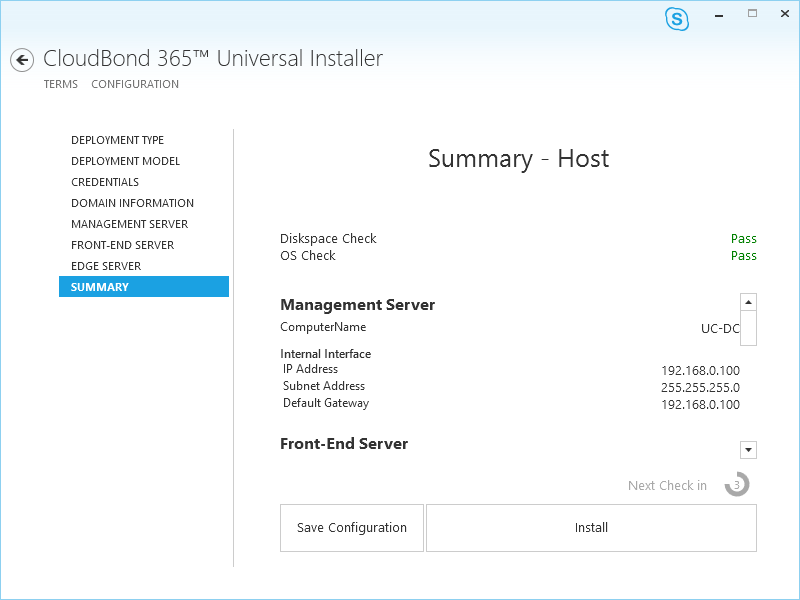
We then get a nice summary showing what the CloudBond is going to build for us.
We can then kick everything off by hitting Install
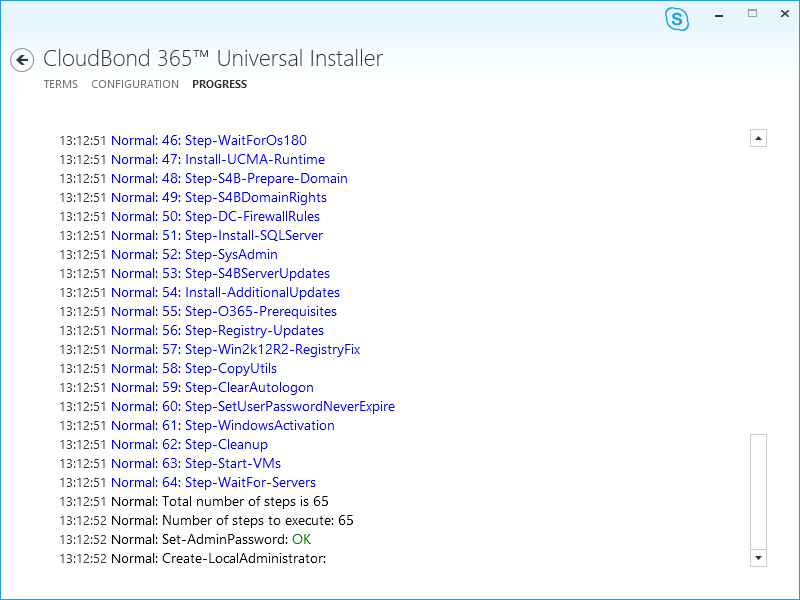
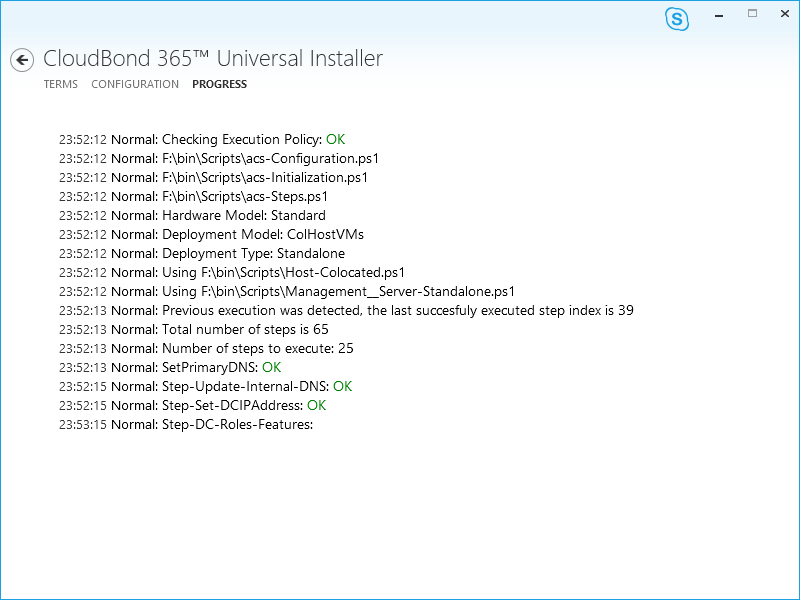
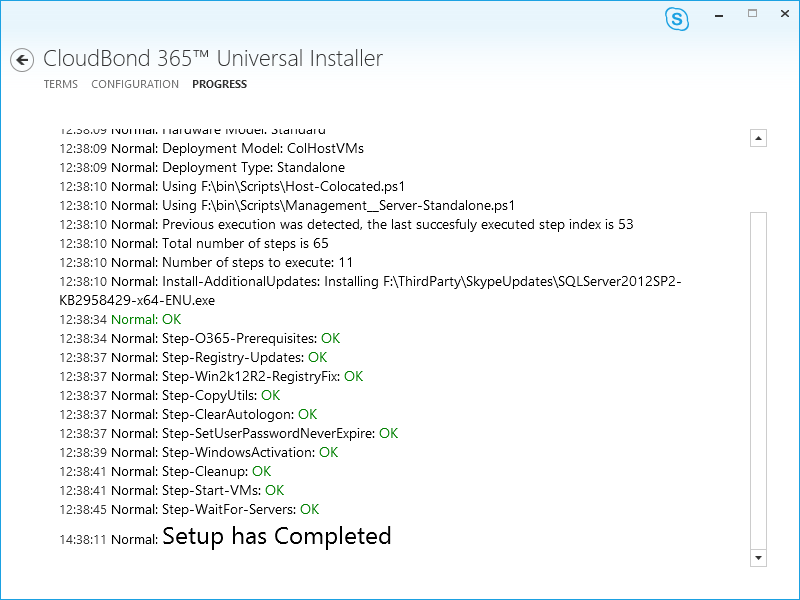
And the build starts, it’s quite normal for the unit to reboot a few times during this process and its usually pretty good at getting things moving by itself. I broke it when I was messing about during installs but all I had to do was manually run Setup.exe from the ISO and the installer just picked up from where it left off.
It broke the time on itself for some reason after a reboot, I quickly fixed this up
Eventually, over an hour (maybe 2, cant remember) it will finish the install
Close the installer and its time to run the console for the first time
Aaaand request / upload your licence key
Aaand that’s where I’m going to leave this part.
Next time we get to play with the web interface and I’ll show off how it makes making some of the more annoying things simpler.
Sorry this took a little longer than expected, but I should be able to pump out part 3 before the end of the year.



Pingback: AudioCodes CloudBond In Depth Review Part 1 | Skype4BAdmin.com
Excellent article, what happened with part 3?
Unfortunatey it took me so long to do part 2 that I had to send the unit back. That along with the fact I’ve changed integrators means we may never see it.. I may address this again in the future. I just need to tee up a time with Audiocodes to okay with their lab.